Social.png attack on Joomla, WordPress and Drupal
Social.png attack on Joomla, WordPress and Drupal
I’m going to write now a rather different type of article, this led me to believe that some of our dear friends, users and whoever thinks he should be involved, are rather stupid people. Why I think that? Its easy enough and you will understand a bit later along this article. From the start, please do not believe I have a thing with these users that I’m going to talk about in this article, no, I don’t even care at this point, I’ll be frank and just point them to this article that I’m going to write.
With that being said, lets begin. I’m going to talk about the recent social.png which *again* has started showing up and that users believe is being injected due to vulnerability in their script or web server.
What type of hack is this?
In a few words, its a social engineered attack. What does this mean? Basically the hacker induced the user to unknowingly download and install that social.png file.
How exactly does this work?
Think of it like this, for popular scripts like Joomla, WordPress or Drupal, there are a lot a components and plugins that you can install for free, however some of them are commercial. Now I completely understand that we do not like paying for something you don’t even know it will work as expected, so what does the user do? Good ol’ google to the rescue and tries to find a similar script that does the same thing as the commercial one.
In this stage, you probably have found the original site that advertised the commercial script you are looking for, but you will probably also find something like
your plugin name free nulled download
So the user quickly navigates, downloads the plugin and sees that it is the same one that was commercially advertised earlier.
Should also contain something like:
|
1 2 3 4 |
Downloaded from nulledsite.com. The best online place for nulled scripts !! Direct downloads no bullshit. |
You think, “so what? Everyone does that…“, true, I admit, in my youthful time I have indeed played with some nulled scripts, however nothing came out of it so I can’t complain and I’ve also grown up since then.
You however, because you have came to this page searching for the social.png, try to find the reason for something that probably messed your website.
What do you think it could be wrong with using nulled scripts? Well I was reading the other day a PDF file on CryptoPHP which actually is the same name for the social.png hack and they pointed out some very interesting things.
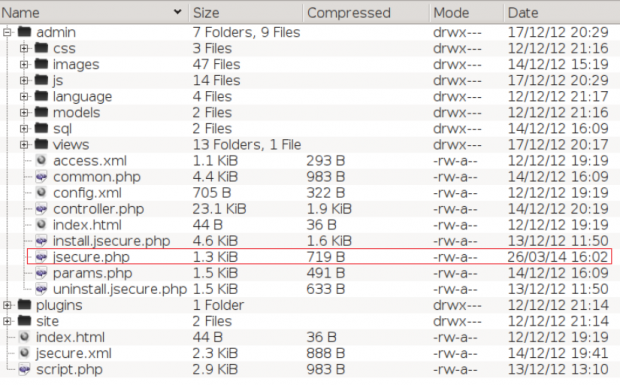
For instance, that free nulled script you believe is safe, is actually a modified version of the original script, for instance the image bellow:
you will see that one specific file has a completely different timestamp than the other files. That’s not so normal, right?
The next image has the same difference in timestamp but with the social.png file.
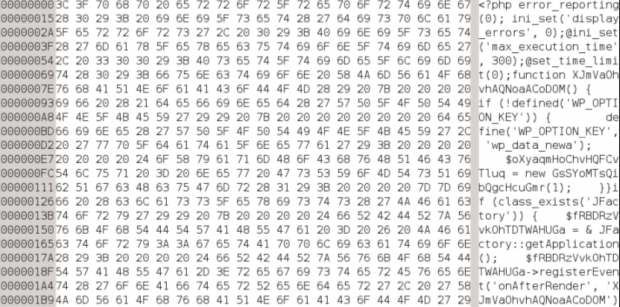
If checking the file jsecure.php you will find a similar code:
|
1 |
<?php include('images/social.png'); ?> |
That in itself is strange !?!? Why would someone in their right mind would include an image in the php file. But if the image is not really an image, that’s a different matter, right?
The social.png file does indeed contain obfuscated content. So the person who included that file, lets say he wasn’t really crazy.
What does this CryptoPHP actually do?
The cryptoPHP will communicate automatically with C2 server (Command and control server) using a public key encryption. It can easily integrate with well known CMSs like WordPress, Joomla, Drupal and inject content into the affected websites. This is usually used by users doing illegal search engine optimization, or Blackhat SEO.
The script is made in a way that it can automatically update itself, so if the hacker wants, he can always add new features to this script so that he can control the affected sites better.
I can talk a lot more about what it can do, but better not give stupid ideas to the wrong people.
So if you finished reading everything, why do you think you had this social.png file that caused all your website issues?
This is not a vulnerability hack, this is a social engineered hack.
The affected user itself uploaded this file into their own website.
With that being said, you users who use nulled version of scripts trying to make a successful website, you are idiots!
Oh I forgot to say something really important, most hacked sites affect the files, databases are usually safe. Of course not all cases are the same. With this type of hack, at least for WordPress sites, a user called *system[NR]*, where NR is a number, is being added to your blog as an admin user. From there you can probably understand the hacker had full access to your site.
I hope this clears out why you got hacked and hopefully you will stop using nulled scripts in the first place.
To users hoping to clean their site, this is not easy, you need to:
- Check the mysql database in case the user *system* has been added, not all versions of social.png do this!
- Make sure you remove the theme, plugin or component that caused this.
- Do a search for any content similar to the png file that contains a string <?php in an image type file or files that have the code
|
1 |
<?php include('social.png'); ?> |
Good luck and hopefully you’ll think twice now.